Virtual Private Cloud Architecture on AWS using Terraform

My name is Joseph Mbatchou, and I am grateful for the opportunity to introduce myself to you.
I have been in the Tech industry for about 8 years, and I am currently performing as Cloud Engineer at CloudSpace Consulting, LLC Manassas, VA.
My journey began as a Computer Science Teacher and Computer Technician at Biopharcam, a computer sales company in my home country. Upon relocating to the United States, I joined Allied Universal, gradually advancing from an officer to a shift lead position. In this role, I oversaw various applications for training and operational tasks, collaborating closely with engineers and developers from Digital Realty, a data center provider.
Observing these professionals at work sparked my interest in cloud computing, leading me to pursue cloud classes, attend boot camps, and conduct in-depth research across various domains, including training at CloudSpace Academy. This exposure deepened my passion for IT and motivated me to transition into the industry to further my personal growth and contribute to organizational success.
As a Cloud Consultant, I have been privileged to collaborate with Cloud Solution Architects and DevOps teams on numerous projects, consistently exceeding customer expectations through our dedication and innovative solutions. My tenure in this role has enriched my skill set and broadened my professional experience.
Now, equipped with a wealth of knowledge in cloud computing and DevOps practices, I am eager to apply my expertise to new challenges and opportunities. I am confident in my ability to contribute effectively to your knowledge
Thank you for considering my hard work. I look forward to have you on board of the learning process.
Virtual Private Cloud Architecture on AWS using Terraform
🚀 Overview:
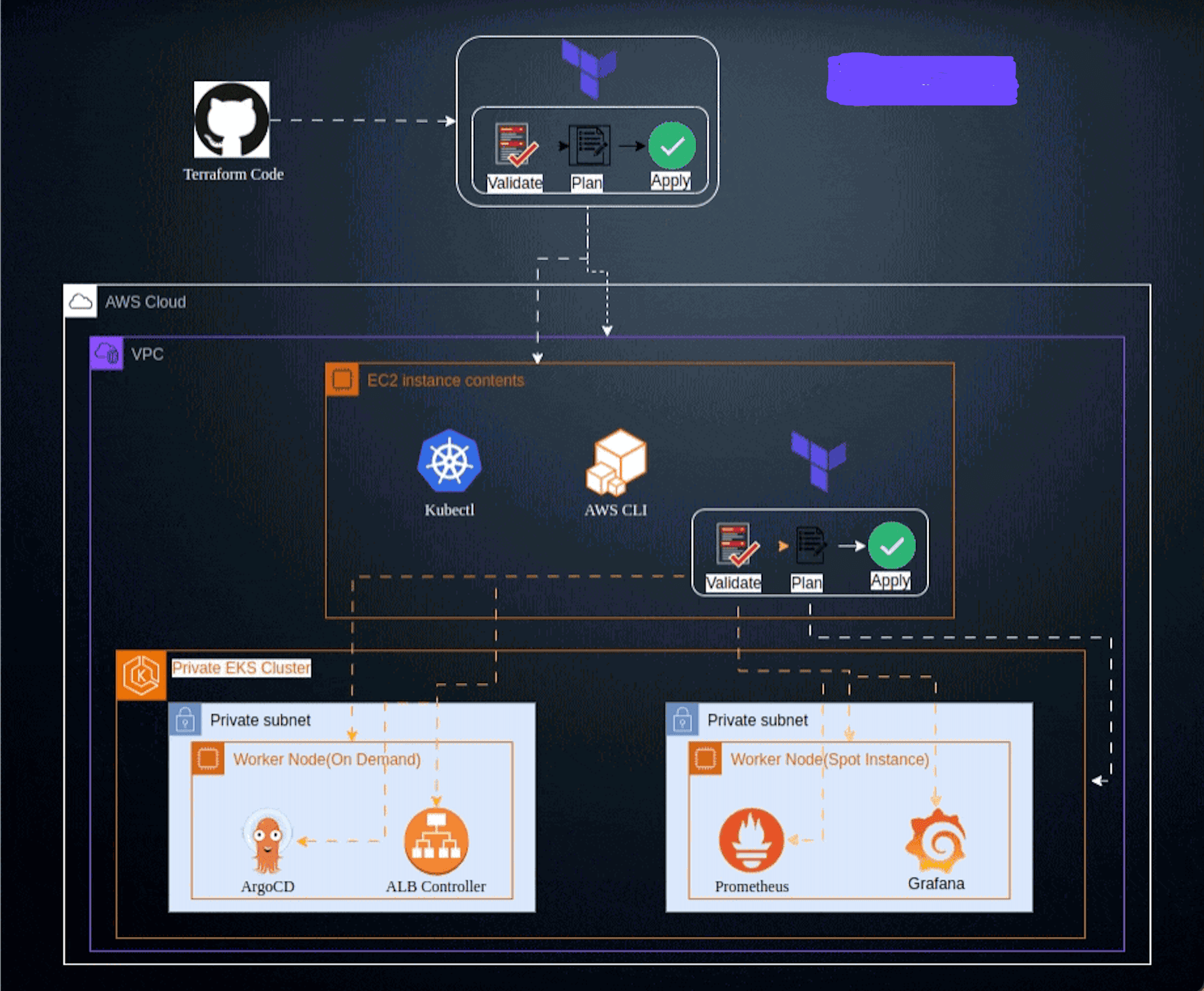
The VPC Architecture project on AWS using Terraform aims to create a scalable and resilient infrastructure that leverages the power of Amazon Web Services (AWS) cloud platform. This project utilizes Terraform, an Infrastructure as Code (IaC) tool, to provision and manage the infrastructure components, enabling automation, repeatability, and scalability. The primary objective of this project is to design and deploy a virtual Private Cloud or Networking architecture on AWS that consists of multiple components, including basement, networking, traffic flow. All components will be deployed across two Availability Zones (AZs) for high availability and fault tolerance.
🔧 Problem Statement
Terraform is an IaC software tool that provides a consistent command line interface (CLI) workflow to manage hundreds of cloud services. Terraform codifies cloud APIs into declarative configuration files. In this specific case you need to create foundation Networking(VPC, Subnets, route table, IGW, NAT Gateway...), Terraform will automatically use the configuration files to provide the infrastructure resources where we can run application needed. Terraform will use his deployment to provide all AWS needed elements avoiding us to use the console and it will automate the setup, ensuring consistency and reducing human error.
💽 Techonology Stack
The architecture consists of the following three tiers:
VPC: AWS VPC
Subnets: AWS Subnets
Route table: AWS route table
NACL: AWS NACL
Internet Gateway: AWS IGW
📌 Architecture Diagram

🌟 Project Requirements
Before you get started, make sure you have the following prerequisites in place:
Terraform installed on your local machine.
AWS IAM credentials configured in your text editor. In this case we will use VSCODE.
Git installed on your local machine and Github account set up Github
Git for cloning the repository.
You must also know Terraform workflow

📋 Table of Contents
I - Terraform Configuration files
Step 1: Provider Configuration
Step 2: Variables Configuration
II - Instructions of Deployment
✨Terraform Configuration files
You need to write different files generating resources
Step 1: Provider Configuration
Here we declare our cloud provider and we specify the region where we will be launching resources
Step 2: Variables Configuration
This is where we declare all variables and their value. It includes
Variables: List of element that can vary or change. They can be reuse values throughout our code without repeating ourselves and help make the code dynamic
values: values attributed to each variables.
We have
Step 3: VPC Configuration
This is where you create the basement, foundation and networking where all the resources will be launch. It includes VPC, Subnets, IGW, NatGateway, EIP and Route tables
We have here
VPC: Virtual Private Cloud the main and private environment where all resources will be launch
Subnets: is a segmented portion of a virtual private cloud (VPC) that allows you to partition your network resources. Subnets are used to organize and manage your cloud resources more effectively by providing isolation and control over network traffic.
Internet Gateway: it plays a crucial role in enabling internet connectivity for resources within a VPC, allowing instances to access services, applications, and data hosted on the public internet while providing scalability, redundancy, and security features.
Route Tables: is a fundamental networking component that controls the routing of network traffic within a Virtual Private Cloud (VPC). Route tables define the rules for directing traffic from one subnet to another or to external networks, such as the internet or on-premises networks.
NCAL: Network Access Control Lists (NACLs) are a security layer in AWS that act as a firewall for controlling traffic in and out of one or more subnets within a Virtual Private Cloud (VPC).
Security Groups: a security group acts as a virtual firewall for controlling inbound and outbound traffic to AWS resources, such as EC2 instances, RDS databases, and other services within a Virtual Private Cloud (VPC). Security groups allow you to define rules that specify the type of traffic allowed or denied based on protocols, ports, and IP addresses.
Step 4: Output Configuration
Know as Output Value : it is a convenient way to get useful information about your infrastructure printed on the CLI. It is showing the ARN, name or ID of a resource. In this case we are bringing out the DNS name of the web application Load balancer.
💼 Instructions of Deployment
Follow these steps to deploy the architecture:
Step 5: Clone Repository:
Clone the repository in your local machine using the command "git clone"
git clone https://github.com/Joebaho/Joebaho-Cloud-Platform/tree/main/site/vpc-foundation-terraform-on-aws
Step 6: Initialize Folder
Initialize the folder containing configuration files that were clone to Terraform and apply the configuration by typing the following command
terraform init
You must see this image

Step 7: Format Files
Apply any changes on files and Review the changes and confirm the good format with command:
terraform fmt
Step 8: Validate Files
Ensure that every files are syntactically valid and ready to go with the command:
terraform validate
If everything is good you will have something like this

Step 9: Plan
Create an execution plan to provide the achievement of the desired state. It Check and confirm the numbers of resources that will be create. Use command:
terraform plan
The list of all resources in stage of creation will appear and you can see all properties(arguments and attributs) of each resources


Step 10: Apply
Bring all desired state resources on life. It Launch and create all resources listed in the configuration files. The command to perform the task is:
terraform apply -auto-approve
Now, the creation will start and you will be able to see which resources is on the way to be create and the time it taking to create.
At the end you will receive a prompt message showing all resources status: created, changed and the numbers of them.

Here are the outputs :

Step 11: Review of resources
Go back on the console and check all actual state resources one by one to see. You will have
- VPC

Subnets

IGW

Route Tables

NCAL

Step 12: Destroy
Destroy the terraform managed infrastructure meaning all resources created will be shut down. This action can be done with the command "terraform destroy"
terraform destroy -auto-approve
At the end you will receive a prompt message showing all resources has been destroyed

🤝 Contributing
Your perspective is valuable! Whether you see potential for improvement or appreciate what's already here, your contributions are welcomed and appreciated. Thank you for considering joining us in making this project even better. Feel free to follow me for updates on this project and others, and to explore opportunities for collaboration. Together, we can create something amazing!
📄 License
This project is licensed under the JoebahoCloud License